Alternatives to Calendar Lock PEA
Google Calendar, Apple Calendar, Microsoft Outlook
When you buy a smartphone or PC, there's usually a calendar application pre-installed. And these calendar applications work well and are easy to use. That's why many people use Google Calendar, Apple Calendar or Microsoft Outlook.
Many people know it, but displace it: Your calendar data is collected and processed for commercial purposes. And calendar data in particular is sensitive. Not only do you deliver your personal appointments, but calendar dates often also contain data about other people.
Privacy Focus
The Calendar Lock PEA tries to protect sensitive calendar data as much as possible. As a result, you have to download an application, enter your password each time you use it, and so on. Other applications choose a different compromise between security and usability, may have more features and other advantages.
While there are a lot of alternatives to the Notebook PEA or the File Lock PEA, alternatives to the Calendar Lock PEA are a rarity. To my knowledge, the Calendar Lock PEA was the first desktop application of its kind end of 2019. But there are now some online calendar applications that also claim security and privacy. Some of these programs offer synchronization between different devices and are certainly superior to the desktop-only application Calendar Lock PEA in terms of applicability.
Tutanota
The mail provider Tutanota has integrated an encrypted calendar into its mail service: Tutanota Secure Calendar.
With the free account a single calendar can be created (when importing other calendars the events will be integrated into this calendar). With the premium account (1 € per month), multiple calendars can be managed and with the team account, entire calendars can be shared. The handling is similarly intuitive on the smartphone and in the browser.
Tutanota is also trying to find a general solution to the problem that the CalDAV protocol prevents calendar data from being privacy protected.
Calendars can be synchronized encrypted between desktop (in browser) and Android/LineageOS or iOS devices.
Calendar Features
Calendars can be exported and imported to include existing calendars from other applications. The using of HTML formatting for the description property makes exported events sometimes hard to read, but the export and import works fine otherwise.
The usual features of the iCalender format are integrated: title, description, location... The recurrence does not allow to define weekdays like every third Monday and Wednesday, recurrences on specific days or exceptions, but the basic settings are implemented.
Security / Crypto
Tutanota's security is mainly based on the password. The mails also include asymmetric cryptography, but you can log in with the password and the mail address alone. A minor additional protection is provided by the list of accesses in the settings - here you can check when and from which device the account was accessed.
Tutanota uses AES-128 for encryption. This is not really state-of-the-art. Symmetric keys of 128 bit are considered secure only for a limited time. That means, if the encrypted data is stored today, it might be decrypted in 10 or 20 years. Nevertheless, this is still widely used and even GPG has only recently switched to longer keys (AES-256) for the default setting.
A minor minus.To derive the key from the password the function bcrypt is used. This is slightly better than many programs that still use the NIST standard PBKDF2. But also bcrypt offers only a very limited protection against attacks with custom hardware, e.g. ASICs. More recent functions such as Scrypt, Argon2 or Catena are memory-hard, to make such attacks as difficult as possible. Since Tutanota‘s security is so password-based, that's a pity. To be fair, it must be said that the standard GPG function used for this pupose (S2K) is even worse in this respect.
So another minor minus.Besides that Tutanota does many things right:
- The encryption takes place on the client side, so it is actually an end-to-end encryption.
- At least the source code of the client side is open - unfortunately not also that of the server side. The company is probably not completely convinced of open source.
- The business model is based on paid accounts, not on advertising or the trade with private user data.
- The company publishes inquiries from law enforcement agencies and deals openly with such threats.
Conclusion: Overall positive.
EteSync
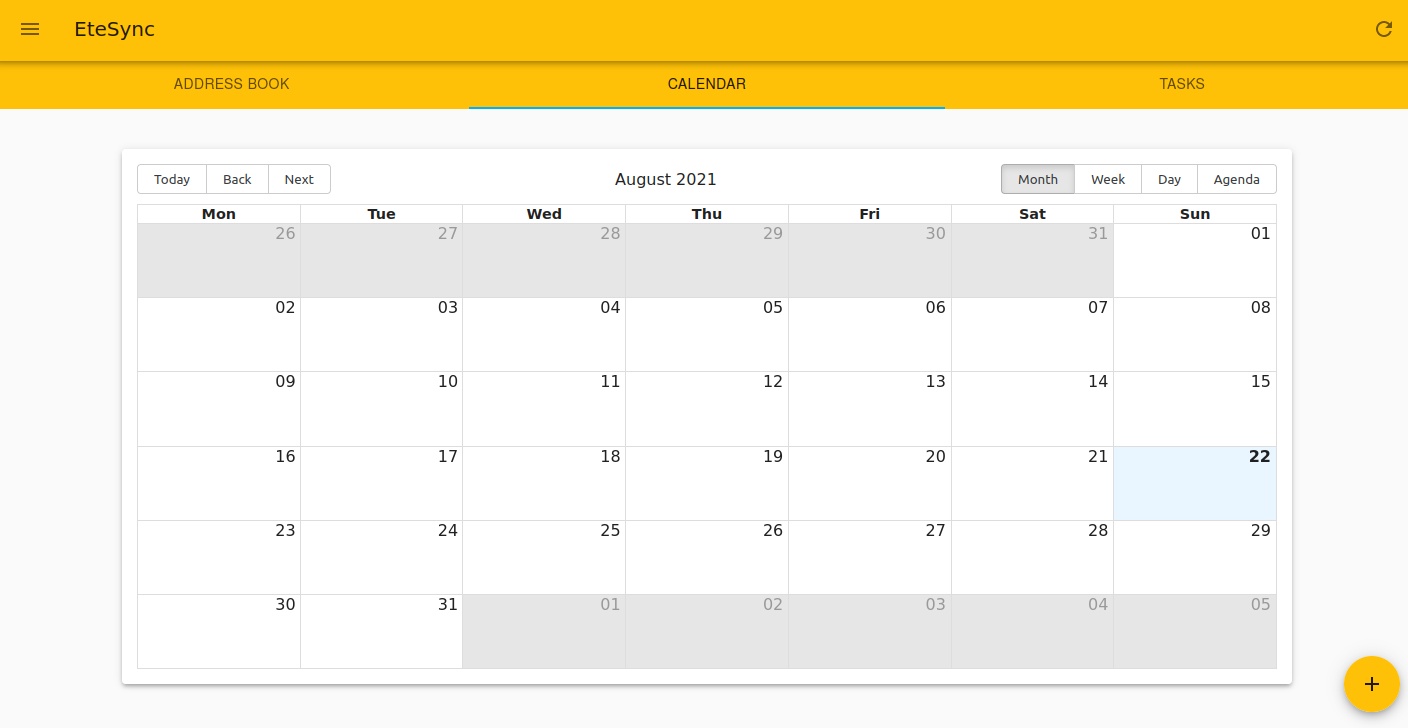
EteSync offers a (paid) end-to-end encrypted calendar for desktop (in browser) and Android/LineageOS or iOS devices: EteSync Calendar.
EteSync has a Warrent Canary, the servers are located in Austria and they use the mail address or username as login-indentifier - not the phone number like many other services, which would be problematic from a privacy point of view.
This is what makes the service likeable.
A downside is that the service is not really cheap (3$ per month), even for private use (as of 2021). For storing usually small amounts of data of calendars and contacts, that is a high price. At least there is the possibility to run your own server with EteSync, as it is completely open source. However, this should not be an option for the vast majority of users.
The pricing policy is also not likeable: free trial account, whose later costs remain unclear at the beginning.
Calendar Features
The calendar is actually clear and has the usual features: title, description, location, even sophisticated repetitions (certain weekdays) in the month are possible. But I did not manage to enter any event, at least not in the browser version in the (free) trial period. This is astonishing.
Security / Crypto
EteSync modified the CalDav and CardDav adapter DAVdroid - encryption was added here, because the CalDav protocol originally does not allow encryption.
As far as I can see, Argon2id with 256 MB is used for key derivation. This is at the cutting edge of cryptography. There is only one downer: The parallel factor, i.e. one core function of Argon2, unfortunately remains unused (is set to 1). This is actually not a security concern, just an unnecessary time consumption: The same security level could be realized in a shorter time.
For encryption XChaCha20 with Poly1305 is used (authenticated encryption with 32 byte key). Thats fine.
Conclusion: EteSync is good from a security point of view. But some issues are irritating.
ProtonCalendar
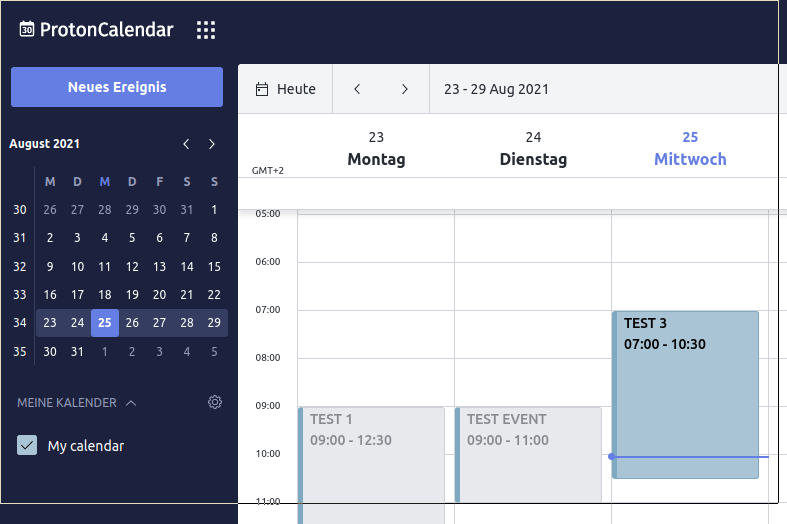
Since April 2021 the mail provider ProtonMail offers an end-to-end encrypted calendar along with their mail service for all accounts:
ProtonCalendar announcementProtonMail has only published the source code step by step, whether everything is actually open source now, I cannot judge. The announcements about the source code releases were always presented in a very spectacular way. The fact that it was only parts of the code that were released could only be inferred from an aside.
The most common calendar properties are implemented, but complicated repetitions, for example, cannot be defined. Usability is intuitive. Import and export of calendars from/to other applications works smoothly.
ProtonMail uses a sophisticated system of asymmetric and symmetric cryptography to keep calendars or events private or share them with others. There is an asymmetric key for every calendar, that is stored encrypted on the server.
I can't really judge the security of ProtonMail calendar. It would take too much time to figure out the system of public, private and symmetric keys for the respective calendar components. The choice of encryption algorithms (AES-256, ECC Curve25519) seems OK.
Bcrypt for password hashing is certainly not the first choice (see also Tutanota), especially if security stands or falls with the password (the asymmetric private keys are stored encrypted on the ProtonMail server - unlike common mail encryption programs). But there is certainly a worse choice.
Protonmail's handling of the conflict with Apple speaks for this company: They did have to give in when Apple blocked updates of ProtonMail and threatened to block the app, but at least they made the story public and didn't just give in quietly.
Also, in another case where a climate activist ended up being arrested, ProtonMail had yielded to the Swiss authorities, but they had at least apologized, made a public statement about it, and recommended the use of Tor.
Conclusion: Looks good.
Peergos Calendar
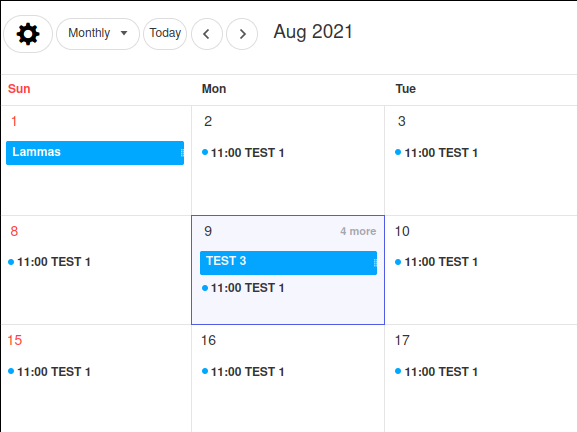
Peergos, a decentralised protocol and open-source platform, announced a calendar:
Peergos Calendar announcementPeergos Security
Peergos Source on GitHub
The service has developed rapidly. The calendar now has many features, such as day, week, month view and more sophisticated recurrence rules.
Security / Crypto
The encryption is based on the memory-intensive key derivation function scrypt, which is a good choice. Asymmetric cryptography is only used to exchange files. Peergos was audited, and the high-priority vulnerabilities found were quickly patched.
Conclusion: The service looks very promising.
Skiff Calendar

Skiff, another open-source platform, announced a calendar:
Skiff CalendarSkiff whitepaper
The program is relatively new and not everything is running smoothly yet, but that could change soon. The service looks promising.