Contact PEA - Free Encrypted Address Book
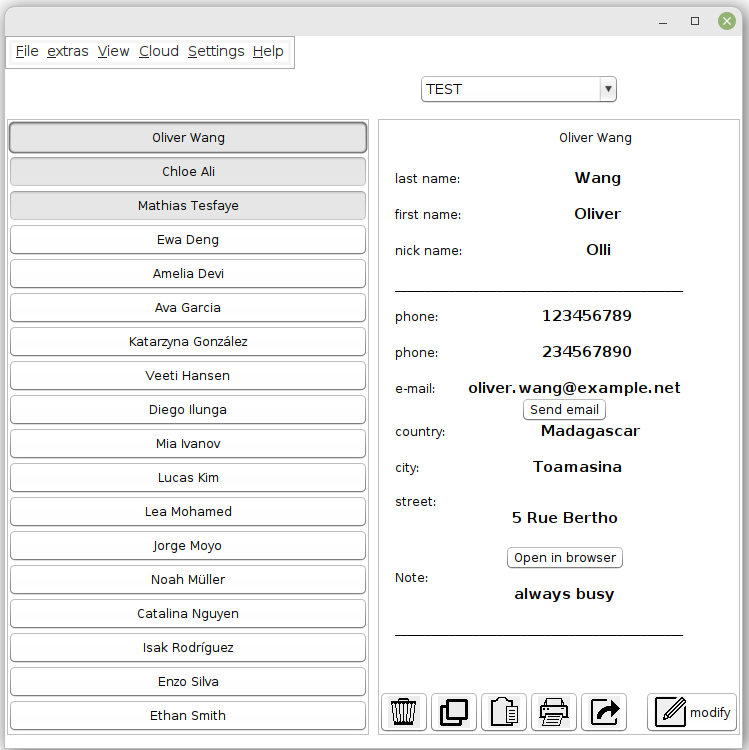
Contact PEA is an easy-to-use open source address book where you can store contacts in a secure way.
Features
Main Features
Privacy Protection
Confidentiality through On-the-fly encryption: The content is decrypted only when requested and only in memory, never on disk.
Cloud Support
Save your calendars in the cloud and upload new versions using several cloud providers. All data remain encrypted during this process.
Authenticated Encryption
Protects the integrity of the data by an authenticated encryption. This guarantees that the data has not been manipulated.
Key File
Add a second factor besides the password and protect your data additionally with a key file. Store this key file wherever you want.
Additional Features
-
Platform independent: Runs on all systems with a Java runtime environment
-
Uses a memory-hard key derivation function that defends custom-hardware attacks
-
All source code is open source, including the libraries used
The program is small and consists of a single archive file. Installation is not required.
How it works
Contacts are organized in address books, where each address book is represented by a file. Decrypted, these files contain contacts in the form of vCards version 4.0 according to the RFC-6350 standard.
When you open an address book, only this one is decrypted and only in memory, not on the hard disk. All others remain encrypted.
Contact Data
Contact data is sensitive data.
When we disclose contact information, we reveal information about others that we have not usually asked permission to disclose. We enable tech companies to collect data about people who don't even use those companies' services. And we have no idea or control over what these companies do with the data.
Creation of profiles
Telephone numbers in particular serve as identification numbers, because in many countries phone numbers cannot easily be anonymized and changing them involves a great deal of effort.
Therefore contacts can be used to merge data from different origins by scammers and data-collecting tech corporations. With an address book entry, for example, the phone number and address can be connected with the accounts on social networks of a person.
Contacts are also the source material for spam, spoofing and phishing emails. Based on contact information, scammers can deceive people into revealing sensitive information, installing malware such as ransomware, or even transferring money.
Encrypting Contacts
Not everyone is willing to enter a password whenever they access their contacts. And the main problem is with mobile phones anyway.
For a local device that only one person uses, it might be overkill. But if you want to store your address book in the cloud, it's grossly negligent not to encrypt it.
Backup of contact data
If we want to realize a minimum of data protection for our mobile devices, it is a good idea to store contact data only locally. This requires a bit of extra effort (see for example Elizas article), but it prevents the tech companies from automatically grabbing all the contact data - as they do by default.
With Contact PEA, not only can a backup be saved securely, but it can also be stored in the cloud - preferably using a locally stored key file. To do this, you just need to import the address book in Contact PEA and protect it with a password.
Encryption at rest
We use only a few of our contacts in daily use. Some contacts we keep for years in the unlikely case that we will eventually need them again. It makes sense to occasionally sort out these contacts from the address book and store them in another place in a safe way.
Contact PEA is a program to keep such contact data as safe as desired. The password, depending on its length, may only protect against casual fraudsters. With the key file placed on another storage medium, a second security factor can be added that meets very high security requirements.
Download Options for Contact PEA 0.5-beta:
Cipher (EAX-Mode): Threefish, AES-256, Serpent
Hash Function: Blake2b, SHA-3, SHA-512
How to use
Start the Jar Archive
You need OpenJDK, Java Runtime Environment (JRE) or something similar (at least 1.8). On most systems there is at least one available.
These PEAs are single Java jar archives, a file with the extension "jar". If you are familiar with jar
archives, you can skip the following part.
Initialization: First Start
The first time you start the Contact PEA, the program will initialize. You are asked for a password
and an address book name.
You can reset the password later in the menu.