Calendar Lock PEA - Free Encrypted iCalendar Application
Calendar Lock PEA is an easy to use open source calendar tool that you can use for keeping track of your events. It includes a customizable month, week and day view where you can edit your appointments, as well as a task manager. The calendars can be stored with various cloud providers.

Features
Main Features
Privacy Protection
Confidentiality through On-the-fly encryption: The content is decrypted only when requested and only in memory, never on disk.
iCalendar Compatibility
Compatible with iCalendar data (ics files), such as those used in Google Calendar, Apple Calendar, Microsoft Outlook and other areas.
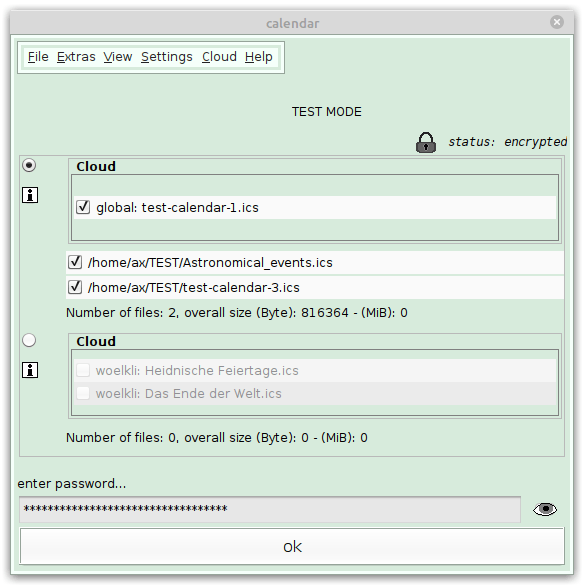
Cloud Support
Save your calendars in the cloud and upload new versions using several cloud providers. All data remain encrypted during this process.
Authenticated Encryption
Protects the integrity of the data by an authenticated encryption. This guarantees that the data has not been manipulated.
Key File
Add a second factor besides the password and protect your data additionally with a key file. Store this key file wherever you want.
Encryption at rest
Separate rarely used data from data in daily use, store them in extra files, and define customized security levels for each type of data.
Additional Features
-
Platform independent: Runs on all systems with a Java runtime environment
-
Uses a memory-hard key derivation function that defends custom-hardware attacks
-
Adjustability for colors, font sizes, calendar view
-
All source code is open source, including the libraries used
-
Measures the quality of new passwords during input by a password strength meter. Indicates their strength by colored bars
-
Combines System Entropy with its own Entropy Source
-
Offers character tables to enlarge the character set of passwords
The program is small and consists of a single archive file. Installation is not required.
Calendar Data and Privacy Issues
Calendar data should always be available and never be lost, which is one reason they are often stored in the cloud.
At the same time, calendars contain very sensitive and personal information: Appointments allow a precise profile of when you are where, after-work events also reveal something about personal preferences and relationships, medical consultations about your health condition... This is why they are a worthwhile target for snooping:
- Many commercial services are trying to access this data to create user profiles.
- Government agencies are trying to gather information about the behavior of potential dissidents.
- Scammers are just buying and selling these data.
It is not just about not giving potential burglars information about when you are not at home. The protection of calendar data is also a social responsibility: often, calendar data not only reveals private information about oneself, but also about others. And a world in which big Internet companies, criminals and intelligence agencies have gigantic amounts of information at their disposal is a scary world for almost everyone.
Calendar Applications and Data Collection
The popular calendars have many features: Automatic synchronization between devices, events or whole calendars can be easily shared with others, emails can be sent automatically, restaurant reservations or hotel bookings are automatically inserted...
But these features come at a high price: Many popular calendar apps not only collect users' event data, but also phone numbers, email addresses, location data, photos, videos, contacts and much more.
Google Calendar
With Google Calendar, a lot of additional data is tapped besides calendar data. Under the somewhat deceptive term Data Safety, these are listed in the AppStore. Google claims in their support: Google Calendar uses data to improve your experience. This is certainly only part of the truth. The fact that Google's business model consists primarily of collecting data is not mentioned.
Apple Calendar
Apple advertises a lot with the encryption of data in the new "Advanced Data Protection". However, encryption only creates confidentiality if the key is held by the user. But Apple has the key and thus the protection from Apple itself is zero. Apple's security claims regarding calendar data and contact data are misleading. Read more: Blog post by Ben Wolford.
Microsoft Outlook
The days when Microsoft only stored data locally on the PC are long gone. This also applies to Outlook calendar data. As it also stated in a response to a user query: There is no way to deny Microsoft access to the data. The only positive point is that Microsoft does not suggest privacy, after all.
The data from Google Calendar, Apple Calendar and Outlook, for example, can be protected from others with a little know-how and effort, but it is not possible to protect them from the companies themselves.
The popular application services are convenient, but their use does not reflect a sense of responsibility. Calendar Lock PEA is not the only way to responsibly handle your own data and that of your relatives. If the Calendar Lock PEA does not meet your expectations, take a look at the Alternatives to Calendar Lock PEA.
Encryption: End-to-End, Client-side, Server-side, On-the-Fly
The term end-to-end encryption does not quite fit here, not even for cloud support, since there is only one end, but it is correct that the data can only be accessed at the user end.
Calendar Lock PEA's technique is client-side encryption: the data is encrypted before it leaves the user and is sent to a cloud server, for example. In contrast, Google, Apple and Outlook calendar encryption - if any - is server-side encryption, which means that the companies hold the keys and they decide who has access to the data and what it is used for.
The Calendar Lock PEA also offers a characteristic that is called on-the-fly encryption. This means that the data on the storage medium always remains encrypted and only the requested data in memory is decrypted. This is easier to use and less error-prone. You don't have to continually encrypt and decrypt the data, and even in case of a system crash, the encryption remains intact.
Security Levels

This application wants to keep the calendar data private. However, greater protection of the data also goes hand in hand with a certain amount of effort. That is why different levels of protection are available:
Lowest Level
If you want the calendar data to be protected only in the cloud and not on your own device, then you can use Calendar Lock PEA like a "normal" application without having to enter the password.To do this, enable the keyfile-only mode during initialization or later in the settings menu (Security settings - Key derivation function - Use only one keyfile...) and then enable the direct start mode (settings menu - Enable the direct start mode).
Highest Level
The best protection is achieved if you create a key file in addition to the password and store it on a removable medium (USB stick, SD card...).The effort is then greater, but to what you know (the password) is added something you own (keyfile on a medium) as a second factor.
Additionally, the parameters for the key derivation function can be increased - causing a longer execution time, but also in a higher hurdle for cracking the password.
Between these two extremes, various gradations are possible. The default configuration is to use a password.
Download Options for Calendar Lock PEA 1.8:
Cipher (EAX-Mode): Threefish, AES-256, Serpent
Hash Function: Blake2b, SHA-3, SHA-512
Acknowledgement
Thanks to all who have improved, tested or reviewed Calendar Lock PEA and other PEAsHow to use
You have problems to start or use the program? Have a look at the manual.If you enjoy Calendar Lock PEA, like it on a or share it on...