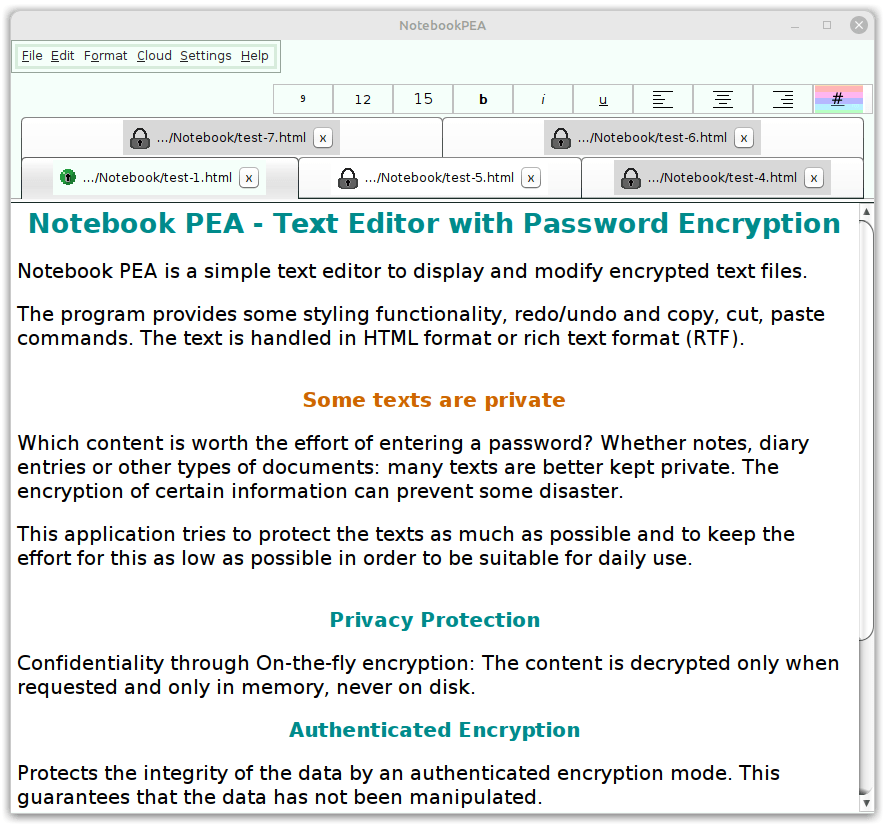
Notebook PEA - Text Editor with Password Encryption
Notebook PEA is a simple text editor to display and modify encrypted text files.
The program provides some styling functionality, redo/undo and copy, cut, paste commands.
The text is handled in HTML format or rich text format (RTF).
Features
Main Features
Privacy Protection
Confidentiality through On-the-fly encryption: The content is decrypted only when requested and only in memory, never on disk.
Authenticated Encryption
Protects the integrity of the data by an authenticated encryption mode. This guarantees that the data has not been manipulated.
Key File
Add a second factor besides the password and protect your data additionally with a key file. Store this key file wherever you want.
Virtual keyboard against Keyloggers
Provides an internal on-screen keyboard to protect against hardware keyloggers as well against some software keyloggers.
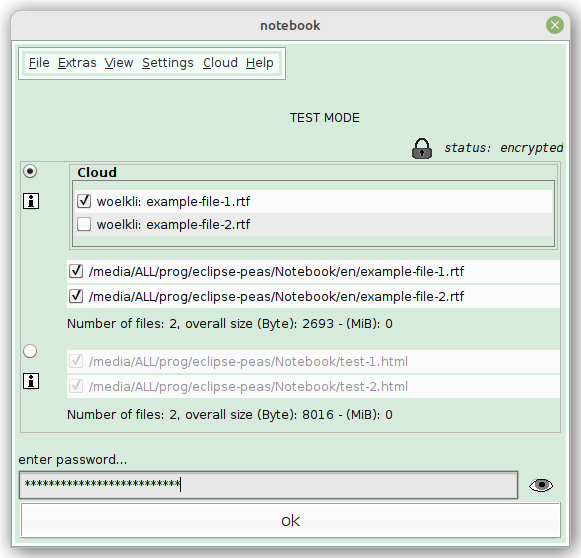
Cloud Support
Save your calendars in the cloud and upload new versions using several cloud providers. All data remain encrypted during this process.
Additional Features
-
Platform independent: Runs on all systems with a Java runtime environment
-
Uses a memory-hard key derivation function that defends custom-hardware attacks
-
Compatible with other programs that use RTF files
-
All source code is open source, including the libraries used
-
Measures the quality of new passwords during input by a password strength meter. Indicates their strength by colored bars
-
Combines System Entropy with its own Entropy Source
-
Offers character tables to enlarge the character set of passwords
The program is small and consists of a single archive file. Installation or registration is not required.
Some texts are private
Which content is worth the effort of entering a password? Whether notes, diary entries or other types of documents: many texts are better kept private. The encryption of certain information can prevent some disaster.
This application tries to protect the texts as much as possible and to keep the effort for this as low as possible in order to be suitable for daily use.
Notebook PEA 1.7:
Key Derivation Function: Catena-Dragonfly, Argon2id, Catena-ButterflyCipher (EAX-Mode): Threefish, AES-256, Serpent
Hash Function: Blake2b, SHA-3, SHA-512
How to use:
There is a manual for the Notebook Pea. Take a look if you can't start or if you have problems to use it.
Version Log:
You can find downloads of old versions and a version log at the versions site .
Alternatives:
If you're unhappy with the notebook PEA, take a look at the alternatives (other open source programs for similar purposes).
Use cases
You can use Notebook PEA for any purpose where texts needed to be encrypted, modified and displayed. However for two scenarios Notebook PEA is not well suited: for communication and as password manager.
Self-Decrypting Archives for Communication
You can use self-decrypting archives like the Notebook PEA for communication, but this is a bad
replacement for public key encryption, which is used for example in GnuPG for mail encryption.
There are mainly two reasons, why self-decrypting archives normally should not be used for communication:
- Most of the passwords are much less secure than (randomly chosen) cryptographic keys. Although it is generally possible to choose secure passwords, in practise this is very rarely the case. In contrast, public key cryptography seems actually secure as long as the keys are long enough.
- You have to share the password. In public key cryptography you can publish your public key, but for self-decrypting archives you have to tell your conversation partner the password first.
Password Managers
It is not necessarily insecure to store and encrypt passwords in a text file. This may be useful as a reminder in case you forget them. But for daily use, password managers are much better suited. There are some good open source password managers available today, so there is no reason to switch to encrypted editors.
Thanks to all who have improved, tested or reviewed Notebook PEA or other PEAs.
Like on a or share on...